[vc_row height=”large” full_height=”1″ us_bg_image_source=”media” us_bg_image=”9071″ us_bg_repeat=”no-repeat” us_bg_parallax=”still” us_bg_overlay_color=”rgba(0,0,0,0.28)” content_placement=”middle” el_class=”home-fisrt-section”][vc_column][vc_row_inner content_placement=”middle”][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22animation-name%22%3A%22afl%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D” width=”1/1″][vc_column_text css=”%7B%22default%22%3A%7B%22font-weight%22%3A%22700%22%7D%7D”]
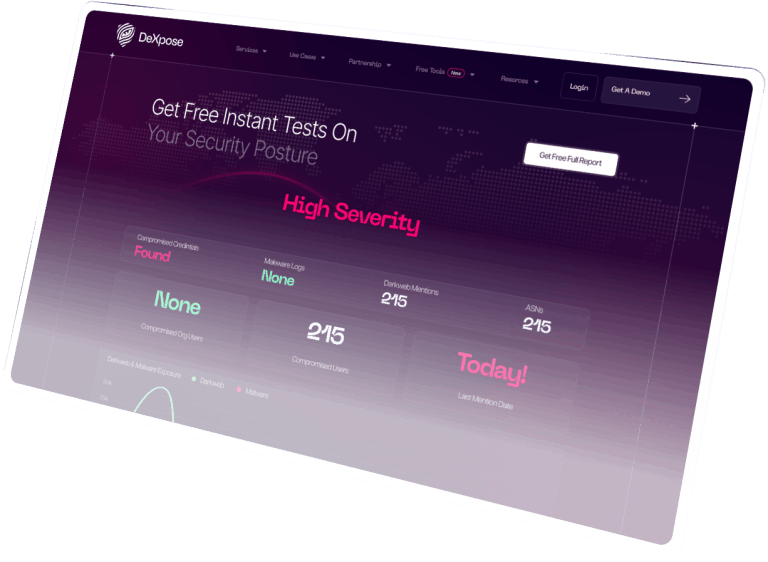
Proactively Fight Cybercrime
[/vc_column_text][us_separator size=”small”][us_itext texts=”Digital Risk Protection
Infostealer Intelligence
Dark Web Monitoring
Attack Surface Mapping
Cybercrime Investigation” tag=”h3″ animation_type=”typingChars” duration=”0.15s” delay=”2s” css=”%7B%22default%22%3A%7B%22font-size%22%3A%2222px%22%2C%22font-family%22%3A%22h1%22%2C%22font-weight%22%3A%22600%22%7D%2C%22laptops%22%3A%7B%22font-size%22%3A%2222px%22%2C%22font-family%22%3A%22h1%22%2C%22font-weight%22%3A%22600%22%7D%2C%22tablets%22%3A%7B%22font-size%22%3A%2222px%22%2C%22font-family%22%3A%22h1%22%2C%22font-weight%22%3A%22600%22%7D%2C%22mobiles%22%3A%7B%22font-size%22%3A%2218px%22%2C%22font-family%22%3A%22h1%22%2C%22font-weight%22%3A%22600%22%7D%7D”][us_separator size=”small”][vc_column_text]
DeXpose gives enterprises and governments the power to investigate cybercrime, monitor the dark web, and uncover compromised data before it’s used against them. Backed by advanced automation and real analysts, we help you stay one step ahead of digital threats.
[/vc_column_text][us_separator size=”small”][us_html]JTNDZGl2JTIwc3R5bGUlM0QlMjJkaXNwbGF5JTNBJTIwZmxleCUzQiUyMGp1c3RpZnktY29udGVudCUzQSUyMGNlbnRlciUzQiUyMiUzRSUwQSUyMCUyMCU1QmdyYXZpdHlmb3JtJTIwaWQlM0QlMjIyJTIyJTVEJTBBJTNDJTJGZGl2JTNF[/us_html][/vc_column_inner][/vc_row_inner][vc_row_inner content_placement=”middle”][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22animation-name%22%3A%22afl%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D” width=”1/1″][us_image image=”14990″ align=”center” size=”full” link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22animation-name%22%3A%22afr%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D”][/vc_column_inner][/vc_row_inner][vc_row_inner content_placement=”middle” css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%2C%22padding-left%22%3A%22%22%2C%22padding-top%22%3A%22%22%2C%22padding-bottom%22%3A%22%22%2C%22padding-right%22%3A%22%22%7D%2C%22laptops%22%3A%7B%22padding-left%22%3A%22%22%2C%22padding-top%22%3A%22%22%2C%22padding-bottom%22%3A%22%22%2C%22padding-right%22%3A%22%22%7D%2C%22tablets%22%3A%7B%22padding-left%22%3A%2210px%22%2C%22padding-top%22%3A%2210px%22%2C%22padding-bottom%22%3A%2210px%22%2C%22padding-right%22%3A%2210px%22%7D%2C%22mobiles%22%3A%7B%22padding-left%22%3A%2210px%22%2C%22padding-top%22%3A%2210px%22%2C%22padding-bottom%22%3A%2210px%22%2C%22padding-right%22%3A%2210px%22%7D%7D” hide_on_states=”default,laptops,tablets,mobiles”][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%7D%7D”][us_hwrapper alignment=”center” link=”%7B%22url%22%3A%22%22%7D”][us_btn label=”Book a Free Demo” link=”%7B%22url%22%3A%22https%3A%2F%2Fleg-b.honeypot.wp.dexpose.io%2Fcontact%2F%22%7D” style=”28″ align=”center”][us_btn label=”Learn More” link=”%7B%22url%22%3A%22https%3A%2F%2Fleg-b.honeypot.wp.dexpose.io%2Fmsps-partnership%2F%22%7D” style=”28″][/us_hwrapper][/vc_column_inner][/vc_row_inner][/vc_column][/vc_row][vc_row height=”large” full_height=”1″ us_bg_image_source=”media” us_bg_image=”9071″ us_bg_repeat=”no-repeat” us_bg_parallax=”still” us_bg_overlay_color=”rgba(0,0,0,0.28)” content_placement=”middle” disable_element=”yes” el_class=”home-fisrt-section”][vc_column][vc_row_inner content_placement=”middle”][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22animation-name%22%3A%22afl%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D” width=”1/2″][vc_column_text]
Proactively Fight Cybercrime
With AI-Powered
[/vc_column_text][us_itext texts=”Physical Security Intelligence
Digital Risk Protect
Cloud Security Posture Management” align=”none” tag=”h3″ animation_type=”typingChars” duration=”0.15s” delay=”2s” css=”%7B%22default%22%3A%7B%22font-size%22%3A%2222px%22%2C%22font-family%22%3A%22h1%22%2C%22font-weight%22%3A%22600%22%7D%7D”][us_separator size=”small”][vc_column_text]Leveraging state-of-the-art automated technologies and human expertise, DeXpose empowers Startups & Enterprises to effortlessly monitor, trace, and prioritize compromised credentials and breaches that could pose a risk to their organization or end users.[/vc_column_text][us_separator size=”small”][us_html]JTVCZ3Jhdml0eWZvcm0lMjBpZCUzRCUyMjIlMjIlMjB0aXRsZSUzRCUyMnRydWUlMjIlNUQ=[/us_html][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” width=”1/2″][us_image image=”9057″ size=”full” link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22animation-name%22%3A%22afr%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D”][/vc_column_inner][/vc_row_inner][vc_row_inner content_placement=”middle” css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%2C%22padding-left%22%3A%22%22%2C%22padding-top%22%3A%22%22%2C%22padding-bottom%22%3A%22%22%2C%22padding-right%22%3A%22%22%7D%2C%22laptops%22%3A%7B%22padding-left%22%3A%22%22%2C%22padding-top%22%3A%22%22%2C%22padding-bottom%22%3A%22%22%2C%22padding-right%22%3A%22%22%7D%2C%22tablets%22%3A%7B%22padding-left%22%3A%2210px%22%2C%22padding-top%22%3A%2210px%22%2C%22padding-bottom%22%3A%2210px%22%2C%22padding-right%22%3A%2210px%22%7D%2C%22mobiles%22%3A%7B%22padding-left%22%3A%2210px%22%2C%22padding-top%22%3A%2210px%22%2C%22padding-bottom%22%3A%2210px%22%2C%22padding-right%22%3A%2210px%22%7D%7D” hide_on_states=”default,laptops,tablets,mobiles”][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%7D%7D”][us_hwrapper alignment=”center” link=”%7B%22url%22%3A%22%22%7D”][us_btn label=”Book a Free Demo” link=”%7B%22url%22%3A%22https%3A%2F%2Fleg-b.honeypot.wp.dexpose.io%2Fcontact%2F%22%7D” style=”28″ align=”center”][us_btn label=”Learn More” link=”%7B%22url%22%3A%22https%3A%2F%2Fleg-b.honeypot.wp.dexpose.io%2Fmsps-partnership%2F%22%7D” style=”28″][/us_hwrapper][/vc_column_inner][/vc_row_inner][/vc_column][/vc_row][vc_row height=”medium” us_bg_image_source=”media” us_bg_repeat=”no-repeat” us_bg_parallax=”vertical” us_bg_parallax_reverse=”1″][vc_column][vc_row_inner css=”%7B%22default%22%3A%7B%22padding-left%22%3A%22100px%22%7D%2C%22laptops%22%3A%7B%22padding-left%22%3A%22100px%22%7D%2C%22tablets%22%3A%7B%22padding-left%22%3A%2280px%22%7D%2C%22mobiles%22%3A%7B%22padding-left%22%3A%2220px%22%7D%7D”][vc_column_inner width=”1/1″][us_text text=”As Seen On” link=”%7B%22url%22%3A%22%22%7D” tag=”h4″ css=”%7B%22default%22%3A%7B%22text-align%22%3A%22left%22%2C%22font-size%22%3A%2218px%22%2C%22line-height%22%3A%2220px%22%2C%22margin-bottom%22%3A%2210px%22%7D%7D”][/vc_column_inner][/vc_row_inner][vc_row_inner columns_gap=”0rem” content_placement=”middle” el_class=”as-seen-on-sec”][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22padding-left%22%3A%220px%22%2C%22padding-right%22%3A%220px%22%7D%7D” width=”1/12″][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22padding-left%22%3A%22-20px%22%2C%22padding-right%22%3A%22-20px%22%7D%2C%22laptops%22%3A%7B%22padding-left%22%3A%22-20px%22%2C%22padding-right%22%3A%22-20px%22%7D%2C%22tablets%22%3A%7B%22padding-left%22%3A%22-20px%22%2C%22padding-right%22%3A%22-20px%22%7D%2C%22mobiles%22%3A%7B%22padding-left%22%3A%220px%22%2C%22padding-right%22%3A%220px%22%7D%7D” width=”2/12″][us_image image=”10276″ align=”center” size=”us_100_100_crop” link=”%7B%22url%22%3A%22%22%7D”][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22padding-left%22%3A%22-20px%22%2C%22padding-right%22%3A%22-20px%22%7D%2C%22laptops%22%3A%7B%22padding-left%22%3A%22-20px%22%2C%22padding-right%22%3A%22-20px%22%7D%2C%22tablets%22%3A%7B%22padding-left%22%3A%22-20px%22%2C%22padding-right%22%3A%22-20px%22%7D%2C%22mobiles%22%3A%7B%22padding-left%22%3A%220px%22%2C%22padding-right%22%3A%220px%22%7D%7D” width=”2/12″][us_image image=”10275″ align=”center” size=”us_100_100_crop” link=”%7B%22url%22%3A%22%22%7D”][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22padding-left%22%3A%22-20px%22%2C%22padding-right%22%3A%22-20px%22%7D%2C%22laptops%22%3A%7B%22padding-left%22%3A%22-20px%22%2C%22padding-right%22%3A%22-20px%22%7D%2C%22tablets%22%3A%7B%22padding-left%22%3A%22-20px%22%2C%22padding-right%22%3A%22-20px%22%7D%2C%22mobiles%22%3A%7B%22padding-left%22%3A%220px%22%2C%22padding-right%22%3A%220px%22%7D%7D” width=”2/12″][us_image image=”10278″ align=”center” size=”us_100_100_crop” link=”%7B%22url%22%3A%22%22%7D”][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22padding-left%22%3A%22-20px%22%2C%22padding-right%22%3A%22-20px%22%7D%2C%22laptops%22%3A%7B%22padding-left%22%3A%22-20px%22%2C%22padding-right%22%3A%22-20px%22%7D%2C%22tablets%22%3A%7B%22padding-left%22%3A%22-20px%22%2C%22padding-right%22%3A%22-20px%22%7D%2C%22mobiles%22%3A%7B%22padding-left%22%3A%220px%22%2C%22padding-right%22%3A%220px%22%7D%7D” width=”2/12″][us_image image=”10277″ align=”center” size=”us_100_100_crop” link=”%7B%22url%22%3A%22%22%7D”][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22padding-left%22%3A%22-20px%22%2C%22padding-right%22%3A%22-20px%22%7D%2C%22laptops%22%3A%7B%22padding-left%22%3A%22-20px%22%2C%22padding-right%22%3A%22-20px%22%7D%2C%22tablets%22%3A%7B%22padding-left%22%3A%22-20px%22%2C%22padding-right%22%3A%22-20px%22%7D%2C%22mobiles%22%3A%7B%22padding-left%22%3A%220px%22%2C%22padding-right%22%3A%220px%22%7D%7D” width=”2/12″][us_image image=”10274″ align=”center” size=”us_100_100_crop” link=”%7B%22url%22%3A%22%22%7D”][/vc_column_inner][vc_column_inner width=”1/12″][/vc_column_inner][/vc_row_inner][us_separator][vc_row_inner content_placement=”middle” css=”%7B%22default%22%3A%7B%22padding-left%22%3A%2230px%22%2C%22padding-right%22%3A%2230px%22%7D%2C%22laptops%22%3A%7B%22padding-left%22%3A%2230px%22%2C%22padding-right%22%3A%2230px%22%7D%2C%22tablets%22%3A%7B%22padding-left%22%3A%2220px%22%2C%22padding-right%22%3A%22%2020px%22%7D%2C%22mobiles%22%3A%7B%22padding-left%22%3A%220px%22%2C%22padding-right%22%3A%220px%22%7D%7D”][vc_column_inner us_bg_overlay_color=”rgba(1,7,42,0.62)” link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-image%22%3A%229730%22%2C%22background-position%22%3A%22center%20center%22%2C%22background-size%22%3A%22contain%22%2C%22background-blend-mode%22%3A%22overlay%22%2C%22background-repeat%22%3A%22no-repeat%22%2C%22backdrop-filter%22%3A%22blur%2810px%29%22%2C%22padding-left%22%3A%2240px%22%2C%22padding-right%22%3A%22%22%2C%22animation-name%22%3A%22afl%22%2C%22animation-delay%22%3A%22250ms%22%7D%2C%22laptops%22%3A%7B%22padding-left%22%3A%2240px%22%2C%22padding-right%22%3A%22%22%7D%2C%22tablets%22%3A%7B%22padding-left%22%3A%2220px%22%2C%22padding-right%22%3A%22%22%7D%2C%22mobiles%22%3A%7B%22padding-left%22%3A%220px%22%2C%22padding-right%22%3A%220px%22%7D%7D” width=”1/2″][us_text text=”UNIFIED CYBER RISK PLATFORM” link=”%7B%22url%22%3A%22%22%7D” tag=”h4″ css=”%7B%22default%22%3A%7B%22color%22%3A%22_content_link_hover%22%2C%22text-align%22%3A%22left%22%2C%22font-size%22%3A%2214px%22%2C%22line-height%22%3A%2220px%22%7D%7D”][vc_column_text]
What We Do
[/vc_column_text][us_separator][vc_column_text]
At DeXpose, we help enterprises and governments investigate cybercrime, uncover hidden threats, and protect their digital presence. Our platform is built to support critical organizations with deep, actionable threat intelligence and real-time visibility into how they’re being targeted—whether through infostealer malware, dark web chatter, or data leaks.
We don’t just collect data – we connect the dots. From tracking cybercriminals to identifying compromised employees and customers, we help you understand the full picture. Whether you’re a national CERT, a financial institution, or a global enterprise, DeXpose equips your team with the tools to investigate, respond, and reduce risk with confidence.
[/vc_column_text][us_separator][us_text text=”Get Safer And Start Today” link=”%7B%22url%22%3A%22https%3A%2F%2Fleg-b.honeypot.wp.dexpose.io%2Fcontact%2F%22%7D” icon=”fas|arrow-right” iconpos=”right”][/vc_column_inner][vc_column_inner us_bg_overlay_color=”rgba(1,7,42,0.62)” link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-image%22%3A%229733%22%2C%22background-position%22%3A%22center%20center%22%2C%22background-size%22%3A%22contain%22%2C%22background-repeat%22%3A%22no-repeat%22%2C%22animation-name%22%3A%22afr%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D” width=”1/2″][us_image image=”14992″ align=”center” link=”%7B%22url%22%3A%22%22%7D”][/vc_column_inner][/vc_row_inner][/vc_column][/vc_row][vc_row css=”%7B%22default%22%3A%7B%22padding-left%22%3A%2250px%22%2C%22padding-right%22%3A%2250px%22%7D%2C%22laptops%22%3A%7B%22padding-left%22%3A%2250px%22%2C%22padding-right%22%3A%2250px%22%7D%2C%22tablets%22%3A%7B%22padding-left%22%3A%2250px%22%2C%22padding-right%22%3A%2250px%22%7D%2C%22mobiles%22%3A%7B%22padding-left%22%3A%2220px%22%2C%22padding-right%22%3A%2220px%22%7D%7D” el_id=”services”][vc_column][us_image image=”9737″ align=”center” size=”us_80_80″ link=”%7B%22url%22%3A%22%22%7D”][vc_column_text]
Built To Scale
[/vc_column_text][vc_column_text css=”%7B%22default%22%3A%7B%22color%22%3A%22%23676A7A%22%2C%22font-size%22%3A%222rem%22%7D%7D”]
As Your Business Grows
[/vc_column_text][us_separator][vc_row_inner columns_gap=”1rem” hide_on_states=”mobiles”][vc_column_inner width=”1/1″][vc_tta_tour layout=”simple2″ switch_sections=”hover” controls_size=”50″ title_font=”h1″ title_transform=”capitalize” title_size=”1.5rem” title_lineheight=”1.7″][vc_tta_section title=”01 Darkweb Monitoring” tab_link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-color%22%3A%22_content_bg_alt%22%2C%22padding-left%22%3A%2230px%22%2C%22padding-top%22%3A%2230px%22%2C%22padding-bottom%22%3A%2230px%22%2C%22padding-right%22%3A%2230px%22%7D%7D” el_class=”homepage-buildtoscale-tabs-darkweb” 1px=”” solid=”” white=”” 8px=””][us_text text=”Darkweb Monitoring” link=”%7B%22url%22%3A%22%22%7D” tag=”h4″ el_class=”text-underline-1″][vc_column_text]Gain comprehensive visibility into your organization’s exposure on the dark web through a 24/7 monitoring service. Stay informed about compromised devices and accounts, ensuring the security of your human and digital assets.[/vc_column_text][us_btn label=”View More Details” link=”%7B%22url%22%3A%22https%3A%2F%2Fleg-b.honeypot.wp.dexpose.io%2Fdarkweb-breaches-monitoring%2F%22%7D” style=”27″ align=”left” icon=”fas|arrow-right” iconpos=”right” css=”%7B%22default%22%3A%7B%22margin-top%22%3A%2220px%22%7D%7D”][/vc_tta_section][vc_tta_section title=”02 Breaches monitoring” tab_link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-color%22%3A%22_content_bg_alt%22%2C%22padding-left%22%3A%2230px%22%2C%22padding-top%22%3A%2230px%22%2C%22padding-bottom%22%3A%2230px%22%2C%22padding-right%22%3A%2230px%22%2C%22border-radius%22%3A%2215px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28219%2C215%2C219%2C0.22%29%22%7D%2C%22laptops%22%3A%7B%22background-color%22%3A%22_content_bg_alt%22%7D%2C%22tablets%22%3A%7B%22background-color%22%3A%22_content_bg_alt%22%7D%2C%22mobiles%22%3A%7B%22background-color%22%3A%22_content_bg_alt%22%7D%7D” el_class=”homepage-buildtoscale-tabs-breaches”][us_text text=”Breaches Monitoring” link=”%7B%22url%22%3A%22%22%7D” tag=”h4″ el_class=”text-underline-2″][vc_column_text]
[/vc_column_text][us_btn label=”View More Details” link=”%7B%22url%22%3A%22https%3A%2F%2Fleg-b.honeypot.wp.dexpose.io%2Fdarkweb-breaches-monitoring%2F%22%7D” style=”27″ align=”left” icon=”fas|arrow-right” iconpos=”right” css=”%7B%22default%22%3A%7B%22margin-top%22%3A%2220px%22%7D%7D”][/vc_tta_section][vc_tta_section title=”03 Attack surface mapping” tab_link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-color%22%3A%22_content_bg_alt%22%2C%22padding-left%22%3A%2230px%22%2C%22padding-top%22%3A%2230px%22%2C%22padding-bottom%22%3A%2230px%22%2C%22padding-right%22%3A%2230px%22%2C%22border-radius%22%3A%2215px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28219%2C215%2C219%2C0.22%29%22%7D%7D” el_class=”homepage-buildtoscale-tabs-attack”][us_text text=”Attack Surface Mapping” link=”%7B%22url%22%3A%22%22%7D” tag=”h4″ el_class=”text-underline-3″][vc_column_text]
[/vc_column_text][/vc_tta_section][vc_tta_section title=”04 Brand Protection” tab_link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-color%22%3A%22_content_bg_alt%22%2C%22padding-left%22%3A%2230px%22%2C%22padding-top%22%3A%2230px%22%2C%22padding-bottom%22%3A%2230px%22%2C%22padding-right%22%3A%2230px%22%2C%22border-radius%22%3A%2215px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28219%2C215%2C219%2C0.22%29%22%7D%7D” el_class=”homepage-buildtoscale-tabs-brand”][us_text text=”Brand Protection” link=”%7B%22url%22%3A%22%22%7D” tag=”h4″ el_class=”text-underline-4″][vc_column_text]Protect your organization from Brand impersonation, Social media impersonation, and Phishing. Our advanced Brand protection services detects potentially fraudulent domains and websites, Social media impersonations,ensuring the Integrity of your brand and security of your employees and valuable clients.[/vc_column_text][us_btn label=”View More Details” link=”%7B%22url%22%3A%22https%3A%2F%2Fleg-b.honeypot.wp.dexpose.io%2Fbrand-protection%2F%22%7D” style=”27″ align=”left” icon=”fas|arrow-right” iconpos=”right” css=”%7B%22default%22%3A%7B%22margin-top%22%3A%2220px%22%7D%7D”][/vc_tta_section][vc_tta_section title=”05 Supply chain monitoring” tab_link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-color%22%3A%22_content_bg_alt%22%2C%22padding-left%22%3A%2230px%22%2C%22padding-top%22%3A%2230px%22%2C%22padding-bottom%22%3A%2230px%22%2C%22padding-right%22%3A%2230px%22%2C%22border-radius%22%3A%2215px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28219%2C215%2C219%2C0.22%29%22%7D%7D” el_class=”homepage-buildtoscale-tabs-supply”][us_text text=”Supply Chain Monitoring” link=”%7B%22url%22%3A%22%22%7D” tag=”h4″ el_class=”text-underline-5″][vc_column_text]Extend your risk protection by monitoring your vendors’ exposure on the dark web. Our comprehensive supply chain dark web monitoring service keeps a vigilant eye on potential threats, ensuring the security and integrity of your organization’s supply chain[/vc_column_text][/vc_tta_section][vc_tta_section title=”Section”][/vc_tta_section][/vc_tta_tour][/vc_column_inner][/vc_row_inner][vc_row_inner columns_gap=”1rem” hide_on_states=”default,laptops,tablets”][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-color%22%3A%22_content_bg_alt%22%2C%22padding-left%22%3A%2230px%22%2C%22padding-top%22%3A%2230px%22%2C%22padding-bottom%22%3A%2230px%22%2C%22padding-right%22%3A%2230px%22%2C%22border-radius%22%3A%2215px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28219%2C215%2C219%2C0.22%29%22%7D%7D” width=”1/5″][us_text text=”Darkweb Monitoring” link=”%7B%22url%22%3A%22%22%7D” tag=”h4″ css=”%7B%22default%22%3A%7B%22font-size%22%3A%2223px%22%7D%7D” el_class=”text-underline-1″][vc_column_text]Gain comprehensive visibility into your organization’s exposure on the dark web through a 24/7 monitoring service. Stay informed about compromised devices and accounts, ensuring the security of your human and digital assets.[/vc_column_text][us_btn label=”View More Details” link=”%7B%22url%22%3A%22https%3A%2F%2Fleg-b.honeypot.wp.dexpose.io%2Fdarkweb-breaches-monitoring%2F%22%7D” style=”27″ align=”left” icon=”fas|arrow-right” iconpos=”right” css=”%7B%22default%22%3A%7B%22margin-top%22%3A%2220px%22%7D%7D”][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-color%22%3A%22_content_bg_alt%22%2C%22padding-left%22%3A%2230px%22%2C%22padding-top%22%3A%2230px%22%2C%22padding-bottom%22%3A%2230px%22%2C%22padding-right%22%3A%2230px%22%2C%22border-radius%22%3A%2215px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28219%2C215%2C219%2C0.22%29%22%7D%7D” width=”1/5″][us_text text=”Breaches Monitoring” link=”%7B%22url%22%3A%22%22%7D” tag=”h4″ css=”%7B%22default%22%3A%7B%22font-size%22%3A%2223px%22%7D%7D” el_class=”text-underline-2″][vc_column_text]Stay ahead of the curve with our continuous monitoring service that scans the latest breached web services. Receive near-realtime alerts on potentially compromised accounts associated with your organization, ensuring prompt action and heightened security.[/vc_column_text][us_btn label=”View More Details” link=”%7B%22url%22%3A%22https%3A%2F%2Fleg-b.honeypot.wp.dexpose.io%2Fdarkweb-breaches-monitoring%2F%22%7D” style=”27″ align=”left” icon=”fas|arrow-right” iconpos=”right” css=”%7B%22default%22%3A%7B%22margin-top%22%3A%2220px%22%7D%7D”][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-color%22%3A%22_content_bg_alt%22%2C%22padding-left%22%3A%2230px%22%2C%22padding-top%22%3A%2230px%22%2C%22padding-bottom%22%3A%2230px%22%2C%22padding-right%22%3A%2230px%22%2C%22border-radius%22%3A%2215px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28219%2C215%2C219%2C0.22%29%22%7D%7D” width=”1/5″][us_text text=”Attack Surface Mapping” link=”%7B%22url%22%3A%22%22%7D” tag=”h4″ css=”%7B%22default%22%3A%7B%22font-size%22%3A%2223px%22%7D%7D” el_class=”text-underline-3″][vc_column_text]Our attack surface mapping service offers a comprehensive overview of your exposed digital assets and services, providing valuable insights to enhance your security posture and mitigate potential risks.[/vc_column_text][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-color%22%3A%22_content_bg_alt%22%2C%22padding-left%22%3A%2230px%22%2C%22padding-top%22%3A%2230px%22%2C%22padding-bottom%22%3A%2230px%22%2C%22padding-right%22%3A%2230px%22%2C%22border-radius%22%3A%2215px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28219%2C215%2C219%2C0.22%29%22%7D%7D” width=”1/5″][us_text text=”Brand Protection” link=”%7B%22url%22%3A%22%22%7D” tag=”h4″ css=”%7B%22default%22%3A%7B%22font-size%22%3A%2223px%22%7D%7D” el_class=”text-underline-4″][vc_column_text]Protect your organization from Brand impersonation, Social media impersonation, and Phishing. Our advanced Brand protection services detects potentially fraudulent domains and websites, Social media impersonations,ensuring the Integrity of your brand and security of your employees and valuable clients.[/vc_column_text][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-color%22%3A%22_content_bg_alt%22%2C%22padding-left%22%3A%2230px%22%2C%22padding-top%22%3A%2230px%22%2C%22padding-bottom%22%3A%2230px%22%2C%22padding-right%22%3A%2230px%22%2C%22border-radius%22%3A%2215px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28219%2C215%2C219%2C0.22%29%22%7D%7D” width=”1/5″][us_text text=”Supply Chain Monitoring” link=”%7B%22url%22%3A%22%22%7D” tag=”h4″ css=”%7B%22default%22%3A%7B%22font-size%22%3A%2223px%22%7D%7D” el_class=”text-underline-5″][vc_column_text]Extend your risk protection by monitoring your vendors’ exposure on the dark web. Our comprehensive supply chain dark web monitoring service keeps a vigilant eye on potential threats, ensuring the security and integrity of your organization’s supply chain[/vc_column_text][/vc_column_inner][/vc_row_inner][/vc_column][/vc_row][vc_row full_height=”1″ v_align=”top” us_bg_image_source=”media” us_bg_image=”9095″ us_bg_repeat=”no-repeat” us_bg_overlay_color=”rgba(1,7,42,0.34)” content_placement=”bottom”][vc_column link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22animation-name%22%3A%22afl%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D” width=”1/2″][vc_row_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22padding-bottom%22%3A%220px%22%7D%2C%22laptops%22%3A%7B%22padding-bottom%22%3A%220px%22%7D%2C%22tablets%22%3A%7B%22padding-bottom%22%3A%2250px%22%7D%2C%22mobiles%22%3A%7B%22padding-bottom%22%3A%22100px%22%7D%7D” width=”1/1″][vc_column_text]
Time To Elevate Your MSP Offerings With Dexpose
[/vc_column_text][us_separator][vc_column_text]Maximize value with our analyst-validated dark web intelligence. Swiftly detect and report for clients. Boost ROI and stand out with our tools, ensuring client peace of mind and setting your MSP apart.
[/vc_column_text][us_separator size=”small”][us_btn label=”Learn More” link=”%7B%22url%22%3A%22https%3A%2F%2Fleg-b.honeypot.wp.dexpose.io%2Fmsps-partnership%2F%22%7D” style=”27″ icon=”fas|arrow-right” iconpos=”right”][/vc_column_inner][/vc_row_inner][/vc_column][vc_column link=”%7B%22url%22%3A%22%22%7D” width=”1/2″][vc_row_inner content_placement=”bottom” css=”%7B%22default%22%3A%7B%22position%22%3A%22absolute%22%2C%22bottom%22%3A%22-130px%22%7D%2C%22laptops%22%3A%7B%22position%22%3A%22absolute%22%2C%22bottom%22%3A%22-80px%22%7D%2C%22tablets%22%3A%7B%22position%22%3A%22%22%2C%22bottom%22%3A%22-50px%22%7D%2C%22mobiles%22%3A%7B%22position%22%3A%22%22%2C%22bottom%22%3A%22-30px%22%7D%7D”][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-color%22%3A%22rgba%286%2C24%2C64%2C0.83%29%22%2C%22padding-left%22%3A%2210px%22%2C%22padding-top%22%3A%2220px%22%2C%22padding-bottom%22%3A%2220px%22%2C%22padding-right%22%3A%2210px%22%2C%22border-radius%22%3A%2220px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28153%2C153%2C153%2C0.38%29%22%7D%7D” width=”1/1″][us_text text=”$10.5 billion bredected loses due to cyber attacks in 2025″ link=”%7B%22url%22%3A%22%22%7D” tag=”h3″ css=”%7B%22default%22%3A%7B%22font-size%22%3A%2220px%22%7D%7D”][vc_column_text]
Since 2020, the amount lost to digital crime has more than doubled. (FBI)
[/vc_column_text][/vc_column_inner][/vc_row_inner][/vc_column][/vc_row][vc_row height=”medium” css=”%7B%22default%22%3A%7B%22background-color%22%3A%22%2301072A%22%7D%7D”][vc_column][vc_row_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-color%22%3A%22%2300001B%22%2C%22background-image%22%3A%229187%22%2C%22padding-left%22%3A%2240px%22%2C%22padding-top%22%3A%2280px%22%2C%22padding-bottom%22%3A%2220px%22%2C%22padding-right%22%3A%2240px%22%2C%22border-radius%22%3A%2220px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22_content_faded%22%2C%22animation-name%22%3A%22afl%22%2C%22animation-delay%22%3A%22250ms%22%7D%2C%22laptops%22%3A%7B%22padding-left%22%3A%2240px%22%2C%22padding-top%22%3A%2280px%22%2C%22padding-bottom%22%3A%2220px%22%2C%22padding-right%22%3A%2240px%22%7D%2C%22tablets%22%3A%7B%22padding-left%22%3A%2240px%22%2C%22padding-top%22%3A%2280px%22%2C%22padding-bottom%22%3A%2220px%22%2C%22padding-right%22%3A%2240px%22%7D%2C%22mobiles%22%3A%7B%22padding-left%22%3A%2220px%22%2C%22padding-top%22%3A%2240px%22%2C%22padding-bottom%22%3A%2220px%22%2C%22padding-right%22%3A%2220px%22%7D%7D” el_class=”box_1″ width=”1/2″][us_text text=”For Integrations” link=”%7B%22url%22%3A%22%22%7D” tag=”h3″][vc_column_text]
Elevate your security stance with our API integration. You can seamlessly incorporate our DarkWeb Monitoring Service, gaining real-time breach detection. Swift alerts, customized reports, and effortless implementation empower you to bolster your cybersecurity posture. Stay ahead of threats and safeguard your digital assets effectively.
[/vc_column_text][us_btn label=”Learn More” link=”%7B%22url%22%3A%22https%3A%2F%2Fleg-b.honeypot.wp.dexpose.io%2Fdarkweb-data-api-integration%2F%22%7D” style=”27″ align=”left” icon=”fas|arrow-right” iconpos=”right”][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-color%22%3A%22%2300001B%22%2C%22padding-left%22%3A%2240px%22%2C%22padding-top%22%3A%2280px%22%2C%22padding-bottom%22%3A%2220px%22%2C%22padding-right%22%3A%2240px%22%2C%22border-radius%22%3A%2220px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22_content_faded%22%2C%22animation-name%22%3A%22afr%22%2C%22animation-delay%22%3A%22250ms%22%7D%2C%22laptops%22%3A%7B%22padding-left%22%3A%2240px%22%2C%22padding-top%22%3A%2280px%22%2C%22padding-bottom%22%3A%2220px%22%2C%22padding-right%22%3A%2240px%22%7D%2C%22tablets%22%3A%7B%22padding-left%22%3A%2240px%22%2C%22padding-top%22%3A%2280px%22%2C%22padding-bottom%22%3A%2220px%22%2C%22padding-right%22%3A%2240px%22%7D%2C%22mobiles%22%3A%7B%22padding-left%22%3A%2220px%22%2C%22padding-top%22%3A%2240px%22%2C%22padding-bottom%22%3A%2220px%22%2C%22padding-right%22%3A%2220px%22%7D%7D” el_class=”red-teamers” el_id=”10897867″ width=”1/2″][us_text text=”For Redteamers” link=”%7B%22url%22%3A%22%22%7D” tag=”h3″][vc_column_text]
Unleash the potential of authentic dark web data in your simulations. Our service equips red teamers with actual compromised credentials and leaked information, enabling you to create scenarios that mirror real-world threats. This authenticity drives more accurate assessments and empowers you to unveil critical vulnerabilities.
[/vc_column_text][us_btn label=”Learn More” link=”%7B%22url%22%3A%22https%3A%2F%2Fleg-b.honeypot.wp.dexpose.io%2Foffensive-security-partnership%2F%22%7D” style=”27″ align=”left” icon=”fas|arrow-right” iconpos=”right”][/vc_column_inner][/vc_row_inner][us_separator css=”%7B%22default%22%3A%7B%22padding-bottom%22%3A%22%22%7D%2C%22laptops%22%3A%7B%22padding-bottom%22%3A%22%22%7D%2C%22tablets%22%3A%7B%22padding-bottom%22%3A%22%22%7D%2C%22mobiles%22%3A%7B%22padding-bottom%22%3A%22%60%22%7D%7D”][vc_row_inner columns_gap=”0rem” content_placement=”middle” css=”%7B%22default%22%3A%7B%22background-repeat%22%3A%22no-repeat%22%2C%22border-radius%22%3A%2220px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%222px%22%2C%22border-top-width%22%3A%222px%22%2C%22border-bottom-width%22%3A%222px%22%2C%22border-right-width%22%3A%222px%22%2C%22border-color%22%3A%22rgba%28153%2C153%2C153%2C0.27%29%22%7D%7D” el_class=”home-for-developers-container”][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-color%22%3A%22%2300001B%22%2C%22padding-left%22%3A%2264px%22%2C%22padding-top%22%3A%2240px%22%2C%22padding-bottom%22%3A%2240px%22%2C%22border-radius%22%3A%2220px%22%7D%2C%22laptops%22%3A%7B%22padding-left%22%3A%2264px%22%2C%22padding-top%22%3A%2240px%22%2C%22padding-bottom%22%3A%2240px%22%7D%2C%22tablets%22%3A%7B%22padding-left%22%3A%2264px%22%2C%22padding-top%22%3A%2240px%22%2C%22padding-bottom%22%3A%2240px%22%7D%2C%22mobiles%22%3A%7B%22padding-left%22%3A%2220px%22%2C%22padding-top%22%3A%2240px%22%2C%22padding-bottom%22%3A%2240px%22%7D%7D” width=”1/2″][us_text text=”For Developers” link=”%7B%22url%22%3A%22%22%7D” tag=”h2″][vc_column_text]
Our developer-friendly APIs provide a straightforward way to enhance your application’s security. Easily incorporate our technology to effortlessly detect and block compromised credentials, ensuring the safety and integrity of user data. Empower your application with cutting-edge protection against threats with minimal effort.
[/vc_column_text][us_btn label=”Learn More” link=”%7B%22url%22%3A%22https%3A%2F%2Fleg-b.honeypot.wp.dexpose.io%2Fdarkweb-data-api-integration%2F%22%7D” style=”27″ align=”left” icon=”fas|arrow-right” iconpos=”right”][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-color%22%3A%22%2300001B%22%2C%22background-image%22%3A%229198%22%2C%22background-position%22%3A%22center%20center%22%2C%22background-size%22%3A%22cover%22%2C%22background-repeat%22%3A%22no-repeat%22%2C%22padding-top%22%3A%2240px%22%2C%22padding-bottom%22%3A%2240px%22%2C%22padding-right%22%3A%2264px%22%2C%22border-radius%22%3A%2220px%22%7D%7D” width=”1/2″][us_image image=”9212″ align=”right” size=”full” link=”%7B%22url%22%3A%22%22%7D”][/vc_column_inner][/vc_row_inner][/vc_column][/vc_row][vc_row][vc_column][vc_row_inner][vc_column_inner width=”1/4″][/vc_column_inner][vc_column_inner width=”1/2″][us_text text=”SIMPLE TO USE” link=”%7B%22url%22%3A%22%22%7D” tag=”h4″ css=”%7B%22default%22%3A%7B%22color%22%3A%22_content_link_hover%22%2C%22text-align%22%3A%22center%22%2C%22font-size%22%3A%2220px%22%7D%7D”][us_text text=”Get Started In 3 Steps” link=”%7B%22url%22%3A%22%22%7D” tag=”h1″ css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%7D%7D”][vc_column_text css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%7D%7D”]
In the blink of an eye, you can check out your organization’s exposure from an adversary perspective.
[/vc_column_text][/vc_column_inner][vc_column_inner width=”1/4″][/vc_column_inner][/vc_row_inner][vc_row_inner content_placement=”middle”][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22padding-left%22%3A%2220px%22%2C%22padding-top%22%3A%2220px%22%2C%22padding-bottom%22%3A%2220px%22%2C%22padding-right%22%3A%2220px%22%2C%22border-radius%22%3A%2220px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28153%2C153%2C153%2C0.38%29%22%2C%22animation-name%22%3A%22afl%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D” width=”2/4″][us_hwrapper stack_on_mobiles=”1″ link=”%7B%22url%22%3A%22%22%7D”][us_vwrapper][us_text text=”1. Get Your Free Report” link=”%7B%22url%22%3A%22%22%7D” tag=”h3″ css=”%7B%22default%22%3A%7B%22text-align%22%3A%22left%22%7D%7D”][vc_column_text css=”%7B%22default%22%3A%7B%22text-align%22%3A%22left%22%7D%7D”]
Get a free instant report summarizing your organization’s exposed secrets. Our non-disruptive approach ensures uninterrupted operations and valuable credential insights.
[/vc_column_text][us_btn label=”FREE DARK WE REPORT” link=”%7B%22url%22%3A%22https%3A%2F%2Fleg-b.honeypot.wp.dexpose.io%2Ffree-darkweb-report%2F%22%7D” style=”28″][/us_vwrapper][us_image image=”9249″ link=”%7B%22url%22%3A%22%22%7D”][/us_hwrapper][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22padding-left%22%3A%2220px%22%2C%22padding-top%22%3A%2240px%22%2C%22padding-bottom%22%3A%2220px%22%2C%22padding-right%22%3A%2220px%22%2C%22border-radius%22%3A%2220px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28153%2C153%2C153%2C0.38%29%22%2C%22animation-name%22%3A%22afr%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D” width=”1/4″][us_text text=”2. Talk To Our Team” link=”%7B%22url%22%3A%22%22%7D” tag=”h3″ css=”%7B%22default%22%3A%7B%22text-align%22%3A%22left%22%7D%7D”][vc_column_text css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%7D%7D”]
Experience DeXpose firsthand by scheduling a demo with our technical team. Discover the comprehensive features of our platform and witness how it can be customized to perfectly align with your specific requirements.
[/vc_column_text][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22padding-left%22%3A%2220px%22%2C%22padding-top%22%3A%2240px%22%2C%22padding-bottom%22%3A%2220px%22%2C%22padding-right%22%3A%2220px%22%2C%22border-radius%22%3A%2220px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28153%2C153%2C153%2C0.38%29%22%2C%22animation-name%22%3A%22afr%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D” width=”1/4″][us_text text=”3. Setup and launch” link=”%7B%22url%22%3A%22%22%7D” tag=”h3″ css=”%7B%22default%22%3A%7B%22text-align%22%3A%22left%22%7D%7D”][vc_column_text css=”%7B%22default%22%3A%7B%22text-align%22%3A%22left%22%7D%7D”]
Within few minutes we will setup your instance, and provide real-time feeds regarding your organization’s dark/deep web exposure through your dashboard. Rest easy knowing we’re keeping you informed and secure.
[/vc_column_text][/vc_column_inner][/vc_row_inner][/vc_column][/vc_row][vc_row height=”auto” css=”%7B%22default%22%3A%7B%22padding-top%22%3A%2280px%22%7D%7D”][vc_column][us_text text=”Why DeXpose” link=”%7B%22url%22%3A%22%22%7D” tag=”h1″ css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%7D%7D”][vc_column_text css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%7D%7D”]
Get free exposure report for your domain name which include markets, malwarelogs and breaches
[/vc_column_text][/vc_column][/vc_row][vc_row columns_gap=”2rem” content_placement=”bottom” css=”%7B%22default%22%3A%7B%22padding-top%22%3A%2210px%22%2C%22padding-bottom%22%3A%22100px%22%7D%2C%22laptops%22%3A%7B%22padding-top%22%3A%2210px%22%2C%22padding-bottom%22%3A%22100px%22%7D%2C%22tablets%22%3A%7B%22padding-top%22%3A%2210px%22%2C%22padding-bottom%22%3A%22100px%22%7D%2C%22mobiles%22%3A%7B%22padding-top%22%3A%2210px%22%2C%22padding-bottom%22%3A%2220px%22%7D%7D”][vc_column link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-color%22%3A%22%23060C2E%22%2C%22padding-left%22%3A%2230px%22%2C%22padding-top%22%3A%2230px%22%2C%22padding-bottom%22%3A%2230px%22%2C%22padding-right%22%3A%2230px%22%2C%22border-radius%22%3A%2220px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28153%2C153%2C153%2C0.38%29%22%2C%22animation-name%22%3A%22afl%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D” width=”1/3″][us_image image=”9187″ align=”center” size=”full” link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22padding-bottom%22%3A%2270px%22%7D%7D”][us_text text=”Sharp Precision” link=”%7B%22url%22%3A%22%22%7D” tag=”h3″ css=”%7B%22default%22%3A%7B%22color%22%3A%22rgb%2824%2C%20187%2C%20236%29%22%2C%22text-align%22%3A%22center%22%2C%22font-size%22%3A%2212px%22%2C%22line-height%22%3A%2218px%22%7D%7D”][us_text text=”Beyond Automation” link=”%7B%22url%22%3A%22%22%7D” tag=”h2″ css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%7D%7D”][vc_column_text css=”%7B%22default%22%3A%7B%22text-align%22%3A%22left%22%7D%7D”]
[/vc_column_text][/vc_column][vc_column link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22animation-name%22%3A%22afr%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D” width=”2/3″][vc_row_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22padding-left%22%3A%2225px%22%2C%22padding-top%22%3A%2240px%22%2C%22padding-bottom%22%3A%2240px%22%2C%22padding-right%22%3A%2225px%22%2C%22border-radius%22%3A%2220px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28153%2C153%2C153%2C0.38%29%22%7D%7D” el_class=”why-dexpose-offensive-security-driven” width=”1/2″][us_text text=”Sharp Precision” link=”%7B%22url%22%3A%22%22%7D” tag=”h3″ css=”%7B%22default%22%3A%7B%22color%22%3A%22rgb%2824%2C%20187%2C%20236%29%22%2C%22text-align%22%3A%22center%22%2C%22font-size%22%3A%2212px%22%2C%22line-height%22%3A%2215px%22%7D%7D”][us_text text=”Offensive Security Driven” link=”%7B%22url%22%3A%22%22%7D” tag=”h4″ css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%2C%22line-height%22%3A%2228px%22%7D%7D”][vc_column_text css=”%7B%22default%22%3A%7B%22text-align%22%3A%22left%22%7D%7D”]
[/vc_column_text][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-color%22%3A%22%23060C2E%22%2C%22padding-left%22%3A%2225px%22%2C%22padding-top%22%3A%2240px%22%2C%22padding-bottom%22%3A%2240px%22%2C%22padding-right%22%3A%2225px%22%2C%22border-radius%22%3A%2220px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28153%2C153%2C153%2C0.38%29%22%7D%7D” el_class=”why-dexpose-deep-investigation” width=”1/2″][us_text text=”Sharp Precision” link=”%7B%22url%22%3A%22%22%7D” tag=”h3″ css=”%7B%22default%22%3A%7B%22color%22%3A%22%23FDCB6E%22%2C%22text-align%22%3A%22center%22%2C%22font-size%22%3A%2212px%22%2C%22line-height%22%3A%2218px%22%7D%7D”][us_text text=”Deep Investigation” link=”%7B%22url%22%3A%22%22%7D” tag=”h4″ css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%7D%7D”][vc_column_text css=”%7B%22default%22%3A%7B%22text-align%22%3A%22left%22%7D%7D”]
[/vc_column_text][/vc_column_inner][/vc_row_inner][us_separator][vc_row_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-color%22%3A%22%23060C2E%22%2C%22padding-left%22%3A%2225px%22%2C%22padding-top%22%3A%2240px%22%2C%22padding-bottom%22%3A%2240px%22%2C%22padding-right%22%3A%2225px%22%2C%22border-radius%22%3A%2220px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28153%2C153%2C153%2C0.38%29%22%7D%7D” el_class=”why-dexpose-perfect-digital-footprint” width=”1/2″][us_text text=”Sharp Precision” link=”%7B%22url%22%3A%22%22%7D” tag=”h3″ css=”%7B%22default%22%3A%7B%22color%22%3A%22%23E84393%22%2C%22text-align%22%3A%22center%22%2C%22font-size%22%3A%2212px%22%2C%22line-height%22%3A%2218px%22%7D%7D”][us_text text=”Perfect Digital Footprint” link=”%7B%22url%22%3A%22%22%7D” tag=”h4″ css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%7D%7D”][vc_column_text css=”%7B%22default%22%3A%7B%22text-align%22%3A%22left%22%7D%7D”]
[/vc_column_text][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22padding-left%22%3A%2225px%22%2C%22padding-top%22%3A%2240px%22%2C%22padding-bottom%22%3A%2240px%22%2C%22padding-right%22%3A%2225px%22%2C%22border-radius%22%3A%2220px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28153%2C153%2C153%2C0.38%29%22%7D%7D” el_class=”why-dexpose-continuous-innovation” width=”1/2″][us_text text=”Sharp Precision” link=”%7B%22url%22%3A%22%22%7D” tag=”h3″ css=”%7B%22default%22%3A%7B%22color%22%3A%22%2300CEC9%22%2C%22text-align%22%3A%22center%22%2C%22font-size%22%3A%2212px%22%2C%22line-height%22%3A%2218px%22%7D%7D”][us_text text=”Continuous Innovation” link=”%7B%22url%22%3A%22%22%7D” tag=”h4″ css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%7D%7D”][vc_column_text css=”%7B%22default%22%3A%7B%22text-align%22%3A%22left%22%7D%7D”]
[/vc_column_text][/vc_column_inner][/vc_row_inner][/vc_column][/vc_row][vc_row][vc_column][vc_row_inner][vc_column_inner width=”1/4″][/vc_column_inner][vc_column_inner width=”1/2″][us_text text=”Get Free Exposure Report” link=”%7B%22url%22%3A%22%22%7D” tag=”h1″ css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%7D%7D”][vc_column_text css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%7D%7D”]
Get free exposure report for your domain name which include markets, malwarelogs and breaches
[/vc_column_text][/vc_column_inner][vc_column_inner width=”1/4″][/vc_column_inner][/vc_row_inner][us_separator size=”small”][us_hwrapper alignment=”center” inner_items_gap=”1.4rem” link=”%7B%22url%22%3A%22%22%7D”][us_image image=”9258″ link=”%7B%22url%22%3A%22%22%7D”][us_image image=”9257″ link=”%7B%22url%22%3A%22%22%7D”][us_image image=”9256″ link=”%7B%22url%22%3A%22%22%7D”][/us_hwrapper][/vc_column][/vc_row][vc_row el_class=”vc-center-content”][vc_column][us_text text=”FAQs” link=”%7B%22url%22%3A%22%22%7D” tag=”h3″ css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%7D%7D”][vc_column_text]
Answers to our frequently asked questions
[/vc_column_text][vc_row_inner el_class=”vc-center-content”][vc_column_inner width=”1/1″][vc_tta_accordion c_icon=”plus” hide_on_states=”default,laptops,tablets,mobiles”][vc_tta_section title=”Who’s Behind DeXpose?” tab_link=”%7B%22url%22%3A%22%22%7D”][vc_column_text el_class=”01-Darkweb-monitoring-tab”]
Our team came from a purely technical background with an average of 10 years of hands-on offensive security experience. We’ve worked with governmental, financial, and other entities to provide TIBER (threat intelligence-based ethical red-teaming) services, among others.
[/vc_column_text][/vc_tta_section][vc_tta_section title=”Can I Monitor Any Assets Through My Account?” tab_link=”%7B%22url%22%3A%22%22%7D”][vc_column_text]
No! Due to the nature of data that deXpose modules can expose. We’re very restrictive when verifying the assets under your authority.
[/vc_column_text][/vc_tta_section][vc_tta_section title=”Will DeXpose Disrupt My Business?” tab_link=”%7B%22url%22%3A%22%22%7D”][vc_column_text]
No, Unless you requested a manual verification and addition of active reconnaissance (Which our team does very carefully), DeXpose is working completely passively and does not interact with your assets.
[/vc_column_text][/vc_tta_section][vc_tta_section title=”Can Other Clients Access My Data?” tab_link=”%7B%22url%22%3A%22%22%7D”][vc_column_text]
No, every client got a dedicated instance that can’t, under any circumstances, interact with other clients’ data.
[/vc_column_text][/vc_tta_section][vc_tta_section title=”Section”][/vc_tta_section][/vc_tta_accordion][us_separator size=”small”][us_text text=”Who’s Behind DeXpose?” link=”%7B%22url%22%3A%22%22%7D” tag=”h3″ css=”%7B%22default%22%3A%7B%22font-size%22%3A%2227px%22%7D%7D”][vc_column_text]
Our team came from a purely technical background with an average of 10 years of hands-on offensive security experience. We’ve worked with governmental, financial, and other entities to provide TIBER (threat intelligence-based ethical red-teaming) services, among others.
[/vc_column_text][us_separator size=”small”][us_text text=”Can I Monitor Any Assets Through My Account?” link=”%7B%22url%22%3A%22%22%7D” tag=”h3″ css=”%7B%22default%22%3A%7B%22font-size%22%3A%2227px%22%7D%7D”][vc_column_text]
No! Due to the nature of data that deXpose modules can expose. We’re very restrictive when verifying the assets under your authority.
[/vc_column_text][us_separator size=”small”][us_text text=”Will DeXpose Disrupt My Business?” link=”%7B%22url%22%3A%22%22%7D” tag=”h3″ css=”%7B%22default%22%3A%7B%22font-size%22%3A%2227px%22%7D%7D”][vc_column_text]
[/vc_column_text][us_separator size=”small”][us_text text=”Can Other Clients Access My Data?” link=”%7B%22url%22%3A%22%22%7D” tag=”h3″ css=”%7B%22default%22%3A%7B%22font-size%22%3A%2227px%22%7D%7D”][vc_column_text]
No, every client got a dedicated instance that can’t, under any circumstances, interact with other clients’ data.
[/vc_column_text][/vc_column_inner][/vc_row_inner][/vc_column][/vc_row]