[vc_row us_bg_image_source=”media” us_bg_image=”9300″ us_bg_size=”contain” us_bg_pos=”bottom center” us_bg_repeat=”no-repeat” us_bg_parallax=”still” us_bg_overlay_color=”rgba(0,0,0,0.34)”][vc_column link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22animation-name%22%3A%22afl%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D” width=”1/1″][vc_row_inner][vc_column_inner width=”1/1″][us_text text=”Protect Your Business with Proactive Dark Web Monitoring” link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22color%22%3A%22%23ffffff%22%2C%22text-align%22%3A%22center%22%2C%22font-size%22%3A%2224px%22%7D%2C%22laptops%22%3A%7B%22color%22%3A%22%23ffffff%22%2C%22text-align%22%3A%22center%22%2C%22font-size%22%3A%2224px%22%7D%2C%22tablets%22%3A%7B%22color%22%3A%22%23ffffff%22%2C%22text-align%22%3A%22center%22%2C%22font-size%22%3A%22%22%7D%2C%22mobiles%22%3A%7B%22color%22%3A%22%22%2C%22text-align%22%3A%22center%22%2C%22font-size%22%3A%22%22%7D%7D”][us_text text=”Dark Web Monitoring” link=”%7B%22url%22%3A%22%22%7D” tag=”h1″ css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%2C%22font-size%22%3A%22200px%22%7D%2C%22laptops%22%3A%7B%22text-align%22%3A%22center%22%2C%22font-size%22%3A%22200px%22%7D%2C%22tablets%22%3A%7B%22text-align%22%3A%22center%22%2C%22font-size%22%3A%22100px%22%7D%2C%22mobiles%22%3A%7B%22text-align%22%3A%22center%22%2C%22font-size%22%3A%2250px%22%7D%7D”][/vc_column_inner][/vc_row_inner][vc_row_inner content_placement=”middle”][vc_column_inner width=”1/6″][/vc_column_inner][vc_column_inner width=”2/3″][vc_column_text]
Understanding The Dark Web
[/vc_column_text][us_separator size=”small”][vc_column_text css=”%7B%22default%22%3A%7B%22color%22%3A%22_header_middle_text_hover%22%7D%7D”]Dark web monitoring is a crucial tool for protecting sensitive information by continuously monitoring illegal online activity. With dark web monitoring services, businesses can proactively identify potential data leaks and take immediate action to prevent catastrophic breaches.
The dark web, a hidden and often untraceable part of the internet, is notorious for hosting illicit activities and markets where stolen data, including compromised credentials, is traded. These compromised login details can be used to gain unauthorized access to your organization’s systems, putting sensitive data at risk. DeXpose’s advanced dark web monitoring system thoroughly scans the dark web’s unindexed corners to determine whether your organization’s credentials are being sold or shared.[/vc_column_text][/vc_column_inner][vc_column_inner width=”1/6″][/vc_column_inner][/vc_row_inner][us_separator][vc_row_inner content_placement=”middle”][vc_column_inner width=”1/6″][/vc_column_inner][vc_column_inner width=”2/6″][us_text text=”Why Should Your Organization Care?” link=”%7B%22url%22%3A%22%22%7D” tag=”h3″ css=”%7B%22default%22%3A%7B%22color%22%3A%22_header_middle_text_hover%22%2C%22font-size%22%3A%2230px%22%7D%7D”][/vc_column_inner][vc_column_inner width=”2/6″][vc_column_text css=”%7B%22default%22%3A%7B%22color%22%3A%22_header_middle_text_hover%22%7D%7D”]Cybercriminals frequently exploit reused credentials from data breaches to gain access to online accounts. This practice is one of the most common ways unauthorized access to business systems is achieved. DeXpose enables you to stay ahead of potential threats by continuously monitoring the dark web for compromised credentials tied to your organization.
By proactively detecting exposed data, DeXpose dark web monitoring helps prevent breaches before they occur, ensuring that unauthorized access is blocked and your organization’s digital security remains intact.[/vc_column_text][/vc_column_inner][vc_column_inner width=”1/6″][/vc_column_inner][/vc_row_inner][/vc_column][/vc_row][vc_row][vc_column width=”1/1″][vc_row_inner][vc_column_inner width=”1/6″][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22padding-left%22%3A%2220px%22%2C%22padding-top%22%3A%2220px%22%2C%22padding-bottom%22%3A%2220px%22%2C%22padding-right%22%3A%2220px%22%2C%22border-radius%22%3A%2215px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28219%2C215%2C219%2C0.51%29%22%2C%22animation-name%22%3A%22afl%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D” width=”2/6″][us_image image=”9463″ has_ratio=”1″ ratio=”3×2″ align=”center” size=”us_90_90″ link=”%7B%22url%22%3A%22%22%7D”][us_separator size=”small”][us_text text=”Data Collection” link=”%7B%22url%22%3A%22%22%7D” tag=”h3″][vc_column_text]DeXpose’s web-crawling technology gathers data from various dark web sources, including underground forums and marketplaces, ensuring comprehensive coverage of potential threats.[/vc_column_text][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22padding-left%22%3A%2220px%22%2C%22padding-top%22%3A%2220px%22%2C%22padding-bottom%22%3A%2220px%22%2C%22padding-right%22%3A%2220px%22%2C%22border-radius%22%3A%2215px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28219%2C215%2C219%2C0.51%29%22%2C%22animation-name%22%3A%22afr%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D” width=”2/6″][us_image image=”9308″ has_ratio=”1″ ratio=”4×3″ link=”%7B%22url%22%3A%22%22%7D”][vc_column_text]
Data Analysis
Our advanced algorithms analyze the collected data to detect any references to your organization’s domain and associated credentials, providing early warnings of potential security risks.[/vc_column_text][/vc_column_inner][vc_column_inner width=”1/6″][/vc_column_inner][/vc_row_inner][us_separator][vc_row_inner content_placement=”middle”][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22padding-left%22%3A%2220px%22%2C%22padding-top%22%3A%2220px%22%2C%22padding-bottom%22%3A%2220px%22%2C%22padding-right%22%3A%2220px%22%2C%22border-radius%22%3A%2215px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28219%2C215%2C219%2C0.23%29%22%2C%22animation-name%22%3A%22afl%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D” width=”1/2″][vc_column_text]Notification[/vc_column_text][us_separator size=”custom” height=”40px” show_line=”1″][vc_column_text css=”%7B%22default%22%3A%7B%22font-size%22%3A%2212px%22%2C%22text-transform%22%3A%22uppercase%22%7D%7D”]A Few seconds ago[/vc_column_text][us_hwrapper inner_items_gap=”0.8rem” link=”%7B%22url%22%3A%22%22%7D”][us_text text=”367 dark web markets mention” link=”%7B%22url%22%3A%22%22%7D” tag=”span” icon=”fas|arrow-right” iconpos=”right” css=”%7B%22default%22%3A%7B%22color%22%3A%22%23ffffff%22%7D%7D”][us_text text=”http://zomato.com” link=”%7B%22url%22%3A%22%20%20http%3A%2F%2Fzomato.com%22%7D” css=”%7B%22default%22%3A%7B%22color%22%3A%22_content_link_hover%22%2C%22font-size%22%3A%2213px%22%7D%7D”][/us_hwrapper][us_hwrapper][us_iconbox icon=”fas|circle” link=”%7B%22url%22%3A%22%22%7D” color=”custom” icon_color=”#ff0a0a” size=”7px” iconpos=”left” alignment=”none”]High (5)[/us_iconbox][us_iconbox icon=”fas|circle” link=”%7B%22url%22%3A%22%22%7D” color=”custom” icon_color=”#ffd60a” size=”7px” iconpos=”left” alignment=”none”]Medium (287)[/us_iconbox][us_iconbox icon=”fas|circle” link=”%7B%22url%22%3A%22%22%7D” color=”custom” icon_color=”#0aff1a” size=”7px” iconpos=”left” alignment=”none”]Low (75)[/us_iconbox][/us_hwrapper][us_separator size=”custom” height=”40px” show_line=”1″][vc_column_text css=”%7B%22default%22%3A%7B%22font-size%22%3A%2212px%22%2C%22text-transform%22%3A%22uppercase%22%7D%7D”]Yesterday – 03:00PM[/vc_column_text][us_hwrapper inner_items_gap=”0.8rem” link=”%7B%22url%22%3A%22%22%7D”][us_text text=”367 dark web markets mention” link=”%7B%22url%22%3A%22%22%7D” tag=”span” icon=”fas|arrow-right” iconpos=”right” css=”%7B%22default%22%3A%7B%22color%22%3A%22%23ffffff%22%7D%7D”][us_text text=”http://zulu.com” link=”%7B%22url%22%3A%22http%3A%2F%2Fzulu.com%22%7D” css=”%7B%22default%22%3A%7B%22color%22%3A%22_content_link_hover%22%2C%22font-size%22%3A%2213px%22%7D%7D”][/us_hwrapper][us_hwrapper][us_iconbox icon=”fas|circle” link=”%7B%22url%22%3A%22%22%7D” color=”custom” icon_color=”#ffd60a” size=”7px” iconpos=”left” alignment=”none”]Medium (2)[/us_iconbox][us_iconbox icon=”fas|circle” link=”%7B%22url%22%3A%22%22%7D” color=”custom” icon_color=”#0aff1a” size=”7px” iconpos=”left” alignment=”none”]Low (10)[/us_iconbox][/us_hwrapper][us_separator size=”custom” height=”30px” show_line=”1″][vc_column_text css=”%7B%22default%22%3A%7B%22font-size%22%3A%2212px%22%2C%22text-transform%22%3A%22uppercase%22%7D%7D”]12 april, 2023 – 01:23 am[/vc_column_text][us_hwrapper inner_items_gap=”0.8rem” link=”%7B%22url%22%3A%22%22%7D”][us_text text=”2 dark web markets mention” link=”%7B%22url%22%3A%22%22%7D” tag=”span” icon=”fas|arrow-right” iconpos=”right” css=”%7B%22default%22%3A%7B%22color%22%3A%22%23ffffff%22%7D%7D”][us_text text=”http://zevendo.com” link=”%7B%22url%22%3A%22http%3A%2F%2Fzevendo.com%22%7D” css=”%7B%22default%22%3A%7B%22color%22%3A%22_content_link_hover%22%2C%22font-size%22%3A%2213px%22%7D%7D”][/us_hwrapper][us_hwrapper][us_iconbox icon=”fas|circle” link=”%7B%22url%22%3A%22%22%7D” color=”custom” icon_color=”#ff0a0a” size=”7px” iconpos=”left” alignment=”none”]High (2)[/us_iconbox][/us_hwrapper][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22animation-name%22%3A%22afr%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D” width=”1/2″][us_text text=”Alert Generation” link=”%7B%22url%22%3A%22%22%7D” tag=”h2″][vc_column_text]Instant Alerts for Compromised Credentials
When compromised credentials are detected on dark web markets or forums, our system generates real-time alerts to notify your security team of the potential breach. This proactive monitoring quickly detects and addresses any exposed data before it can be used maliciously.
How It Works:
- Immediate Notification: As soon as a potential threat is identified, you’ll receive an alert with detailed information, including the severity of the breach (High, Medium, Low).
- Clear Indicators: Alerts include color-coded severity markers to help prioritize the response — Red for High, Yellow for Medium, and Green for Low.
- Actionable Insights: Each alert links to the source, giving you direct access for further investigation and analysis, enabling your team to act quickly and effectively.
- Real-Time Alerts: With continuous scanning of dark web markets, your business remains aware of any potential threats to your credentials and sensitive data, preventing costly breaches.
Keep ahead of cyber threats at all times with our alert generation system, designed to give your team the critical information needed to protect your business from compromised data.[/vc_column_text][/vc_column_inner][/vc_row_inner][/vc_column][/vc_row][vc_row][vc_column link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22animation-name%22%3A%22afl%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D” width=”1/1″][vc_row_inner][vc_column_inner width=”1/6″][/vc_column_inner][vc_column_inner width=”2/3″][us_text text=”Advanced Dashboard Features” link=”%7B%22url%22%3A%22%22%7D” tag=”h2″ css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%7D%7D”][us_text text=”For Comprehensive Dark Web Monitoring” link=”%7B%22url%22%3A%22%22%7D” tag=”h2″ css=”%7B%22default%22%3A%7B%22color%22%3A%22rgba%28219%2C215%2C219%2C0.46%29%22%2C%22text-align%22%3A%22center%22%7D%7D”][vc_column_text]
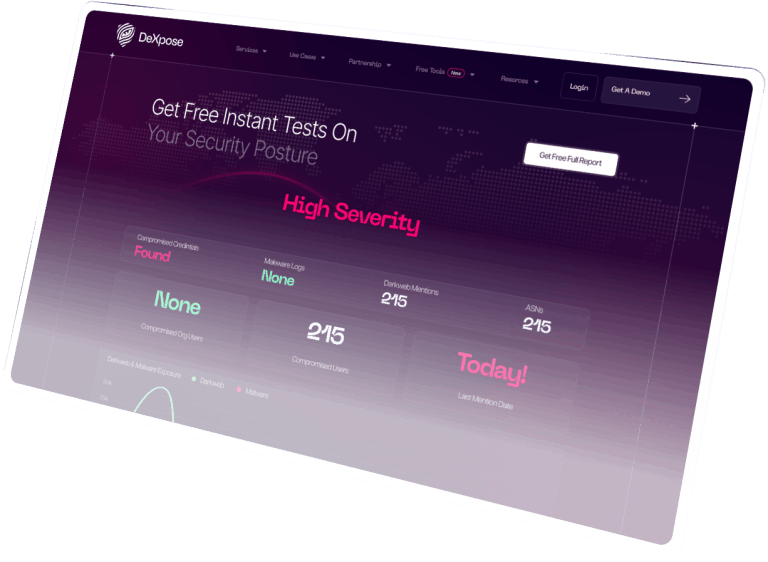
DeXpose offers an intuitive, powerful dark web monitoring dashboard with a variety of features that give you unparalleled control and insight into your organization’s digital security. From monitoring compromised credentials across various user segments to proactively identifying potential breaches, our dashboard empowers you to take swift action and stay ahead of cyber threats.
[/vc_column_text][/vc_column_inner][vc_column_inner width=”1/6″][/vc_column_inner][/vc_row_inner][us_separator][vc_row_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22animation-name%22%3A%22afc%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D” width=”1/1″][us_image image=”9326″ align=”center” size=”full” link=”%7B%22url%22%3A%22%22%7D”][/vc_column_inner][/vc_row_inner][us_separator][vc_row_inner][vc_column_inner width=”1/2″][us_iconbox icon=”far|globe” link=”%7B%22url%22%3A%22%22%7D” title=”Multi-Domain Monitoring for Enhanced Security” title_tag=”h3″ style=”outlined” color=”custom” icon_color=”#ffffff” circle_color=”rgba(227,229,232,0.22)” size=”1.6rem” iconpos=”left” alignment=”none” css=”%7B%22default%22%3A%7B%22animation-name%22%3A%22afc%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D”]Stay on top of your organization’s digital footprint effortlessly. Our dashboard enables you to monitor all domains associated with your business from a single, centralized interface. This ensures that no potential security gaps go unnoticed.[/us_iconbox][/vc_column_inner][vc_column_inner width=”1/2″][us_iconbox icon=”far|envelope” link=”%7B%22url%22%3A%22%22%7D” title=”VIP Personal Email Monitoring” title_tag=”h3″ style=”outlined” color=”custom” icon_color=”#ffffff” circle_color=”rgba(227,229,232,0.22)” size=”1.6rem” iconpos=”left” alignment=”none” css=”%7B%22default%22%3A%7B%22animation-name%22%3A%22afc%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D”]Protecting your organization’s critical communications is vital. Our dashboard extends dark web monitoring to include VIP personal email addresses, safeguarding sensitive personal and business-related data against breaches. This feature ensures your most valuable assets, including executive-level emails, remain secure.[/us_iconbox][/vc_column_inner][/vc_row_inner][us_separator][vc_row_inner][vc_column_inner width=”1/2″][us_iconbox icon=”far|user” link=”%7B%22url%22%3A%22%22%7D” title=”End-User Focus for Holistic Security” title_tag=”h3″ style=”outlined” color=”custom” icon_color=”#ffffff” circle_color=”rgba(227,229,232,0.22)” size=”1.6rem” iconpos=”left” alignment=”none” css=”%7B%22default%22%3A%7B%22animation-name%22%3A%22afc%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D”]DeXpose goes beyond monitoring employee credentials by offering protection for all end users, including partners, clients, and customers. Our platform ensures comprehensive monitoring of compromised credentials across your entire network, leaving no entry point vulnerable.[/us_iconbox][/vc_column_inner][vc_column_inner width=”1/2″][us_iconbox icon=”fas|share” link=”%7B%22url%22%3A%22%22%7D” title=”Vendor And Supply Chain Risk View” title_tag=”h3″ style=”outlined” color=”custom” icon_color=”#ffffff” circle_color=”rgba(227,229,232,0.22)” size=”1.6rem” iconpos=”left” alignment=”none” css=”%7B%22default%22%3A%7B%22animation-name%22%3A%22afc%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D”]Securing your organization means securing your extended network. The DeXpose dashboard includes a vendor and supply chain risk view, allowing you to identify weak links in your cybersecurity chain. This feature helps you monitor third-party vendors and contractors to prevent potential risks from external sources.[/us_iconbox][/vc_column_inner][/vc_row_inner][us_separator][vc_row_inner][vc_column_inner width=”1/2″][us_iconbox icon=”far|thumbs-up” link=”%7B%22url%22%3A%22%22%7D” title=”Actionable Insights” title_tag=”h3″ style=”outlined” color=”custom” icon_color=”#ffffff” circle_color=”rgba(227,229,232,0.22)” size=”1.6rem” iconpos=”left” alignment=”none” css=”%7B%22default%22%3A%7B%22animation-name%22%3A%22afc%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D”]Our platform not only provides dark web monitoring alerts but also delivers actionable insights. Once compromised credentials are detected, you can immediately manage the response and take swift action to mitigate the threat, keeping your organization secure and operational.[/us_iconbox][/vc_column_inner][vc_column_inner width=”1/2″][us_iconbox icon=”fas|file-check” link=”%7B%22url%22%3A%22%22%7D” title=”Customizable Reports” title_tag=”h3″ style=”outlined” color=”custom” icon_color=”#ffffff” circle_color=”rgba(227,229,232,0.22)” size=”1.6rem” iconpos=”left” alignment=”none” css=”%7B%22default%22%3A%7B%22animation-name%22%3A%22afc%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D”]Stay informed with customizable reports tailored to your specific needs. DeXpose allows you to generate daily, weekly, and monthly reports that summarize compromised credentials detected, actions taken, and potential threats mitigated, making it easy to communicate with both executive and technical teams.[/us_iconbox][/vc_column_inner][/vc_row_inner][/vc_column][/vc_row][vc_row][vc_column width=”1/1″][vc_row_inner][vc_column_inner width=”1/6″][/vc_column_inner][vc_column_inner width=”2/3″][vc_column_text]
With DeXpose’s advanced dashboard, your organization gains not only a monitoring tool but a comprehensive, proactive shield against cyber threats. Empower your security strategy today by leveraging the full potential of our dark web monitoring solution and keep your digital assets protected in an increasingly complex cyber landscape.
[/vc_column_text][/vc_column_inner][vc_column_inner width=”1/6″][/vc_column_inner][/vc_row_inner][us_separator][vc_row_inner content_placement=”middle”][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” width=”1/6″][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22padding-left%22%3A%2220px%22%2C%22padding-top%22%3A%2220px%22%2C%22padding-bottom%22%3A%2220px%22%2C%22padding-right%22%3A%2220px%22%2C%22border-radius%22%3A%2215px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28219%2C215%2C219%2C0.51%29%22%2C%22animation-name%22%3A%22afl%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D” width=”2/6″][us_image image=”9345″ size=”full” link=”%7B%22url%22%3A%22%22%7D”][us_text text=”Reputation Protection” link=”%7B%22url%22%3A%22%22%7D” tag=”h3″ css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%7D%7D”][vc_column_text]Safeguard your organization’s reputation by preventing leaks of sensitive information.[/vc_column_text][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-image%22%3A%229346%22%2C%22background-position%22%3A%22center%20center%20%22%2C%22background-size%22%3A%22%22%2C%22background-repeat%22%3A%22no-repeat%22%2C%22height%22%3A%22%22%2C%22animation-name%22%3A%22afr%22%2C%22animation-delay%22%3A%22250ms%22%7D%2C%22laptops%22%3A%7B%22height%22%3A%22%22%7D%2C%22tablets%22%3A%7B%22height%22%3A%22%22%7D%2C%22mobiles%22%3A%7B%22height%22%3A%22300px%22%7D%7D” width=”2/6″][us_text text=”Compliance” link=”%7B%22url%22%3A%22%22%7D” tag=”h3″ css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%7D%7D”][vc_column_text]
Strengthen compliance efforts by actively monitoring and addressing security vulnerabilities.
[/vc_column_text][/vc_column_inner][vc_column_inner width=”1/6″][/vc_column_inner][/vc_row_inner][us_separator][vc_row_inner content_placement=”bottom”][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” width=”1/6″][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22background-image%22%3A%229350%22%2C%22background-position%22%3A%22Center%20Center%22%2C%22background-size%22%3A%22cover%22%2C%22background-repeat%22%3A%22no-repeat%22%2C%22height%22%3A%22%22%2C%22animation-name%22%3A%22afl%22%2C%22animation-delay%22%3A%22250ms%22%7D%2C%22laptops%22%3A%7B%22height%22%3A%22%22%7D%2C%22tablets%22%3A%7B%22height%22%3A%22%22%7D%2C%22mobiles%22%3A%7B%22height%22%3A%22300px%22%7D%7D” width=”2/6″][vc_column_text]Prevent unauthorized access and data breaches by securing accounts linked to compromised credentials.[/vc_column_text][/vc_column_inner][vc_column_inner link=”%7B%22url%22%3A%22%22%7D” css=”%7B%22default%22%3A%7B%22padding-left%22%3A%2220px%22%2C%22padding-top%22%3A%2220px%22%2C%22padding-bottom%22%3A%2220px%22%2C%22padding-right%22%3A%2220px%22%2C%22border-radius%22%3A%2215px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%221px%22%2C%22border-top-width%22%3A%221px%22%2C%22border-bottom-width%22%3A%221px%22%2C%22border-right-width%22%3A%221px%22%2C%22border-color%22%3A%22rgba%28219%2C215%2C219%2C0.51%29%22%2C%22animation-name%22%3A%22afr%22%2C%22animation-delay%22%3A%22250ms%22%7D%7D” width=”2/6″][us_image image=”9349″ size=”full” link=”%7B%22url%22%3A%22%22%7D”][us_text text=”Proactive Security” link=”%7B%22url%22%3A%22%22%7D” tag=”h3″ css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%7D%7D”][vc_column_text]Stay ahead of cyber threats by identifying compromised credentials before they are misused.
[/vc_column_text][/vc_column_inner][vc_column_inner width=”1/6″][/vc_column_inner][/vc_row_inner][/vc_column][/vc_row][vc_row height=”small”][vc_column width=”1/6″][/vc_column][vc_column width=”2/3″][vc_column_text]
DeXpose’s dark web and compromised credentials monitoring service empowers your organization to take proactive measures against potential cyber threats. By staying vigilant and promptly addressing compromised credentials, you can ensure the safety of your sensitive data and maintain your reputation in an increasingly interconnected digital landscape.
[/vc_column_text][/vc_column][vc_column width=”1/6″][/vc_column][/vc_row][vc_row height=”small”][vc_column width=”1/6″][/vc_column][vc_column width=”2/3″][vc_column_text]
Why is Dark Web Monitoring Important for Your Business?
The dark web acts as a concealed marketplace for cybercriminals to sell stolen personal, financial, and corporate data. Without dark web monitoring, your business might not be aware of data leaks until it’s too late. Here’s why dark web monitoring is a critical component of a comprehensive cybersecurity strategy:
- Credentials Leak Detection: Detects when employee or customer credentials are compromised and traded on dark web forums.
- Data Leak Prevention: Proactively identify and prevent data leaks before malicious actors exploit them.
- Insider Threat Monitoring: Track and monitor the sale of sensitive information that disgruntled or malicious insiders may have obtained.
- Deep Web Scanning: Unlike standard search engines, the dark web remains hidden from most search engines, making it more difficult to detect and address breaches without specialized scanning tools.
By implementing dark web monitoring for your business, you gain access to the intelligence needed to protect your organization from identity theft, fraud, and other cybercrimes stemming from stolen data.[/vc_column_text][us_separator][vc_row_inner][vc_column_inner width=”1/1″][vc_column_text]
How Does Dark Web Monitoring Work?
Dark web monitoring tools continuously scan hidden forums, marketplaces, and chat rooms for specific identifiers such as email addresses, credit card numbers, and domain names associated with your business. When any of these identifiers are detected on dark web platforms, dark web monitoring services will alert you immediately, allowing your team to take swift action to mitigate the potential damage.
Some key features of effective dark web monitoring tools include:
- Real-time Alerts: Get instant notifications when sensitive data, such as personal information or corporate credentials, is found on the dark web.
- Comprehensive Coverage: Scan a wide range of dark web sources, including underground forums, black markets, and social networks.
- Historical Data Monitoring: Identify previously exposed data from past incidents that may not have been detected earlier.
- Customizable Alerts: Set specific keywords, domains, or identifiers to receive tailored alerts that matter most to your business.
[/vc_column_text][/vc_column_inner][/vc_row_inner][us_separator][vc_row_inner][vc_column_inner width=”1/1″][vc_column_text]
Why Choose Our Dark Web Monitoring Services?
At Dexpose, we provide the best dark web monitoring services for businesses, designed to deliver comprehensive protection against data breaches and fraud. Here’s why our dark web monitoring solution stands out:
- Proactive Protection: We provide continuous, automated monitoring of the dark web to keep your business protected 24/7.
- Advanced Deep Web Scanning: Our tools scan both the dark web and deep web to ensure no data slips through the cracks.
- Credential Leak Detection: We monitor for compromised user credentials, giving you peace of mind that sensitive data is safe.
- Actionable Alerts: Receive timely, actionable alerts to mitigate threats before they escalate.
[/vc_column_text][/vc_column_inner][/vc_row_inner][us_separator][vc_column_text]
Protect Your Business Today with Dexpose
Cyber threats are lurking in the shadows of the dark web. Please don’t wait until it’s too late to protect your business from a data breach. With our dark web monitoring service, you can secure your business’s sensitive information and gain the peace of mind that comes from knowing you’re actively monitoring and mitigating potential risks.
Contact Dexpose now to learn more about our dark web monitoring solutions and how they can benefit your business. Don’t leave your data exposed—act now and safeguard your organization with the best dark web monitoring tools available.[/vc_column_text][/vc_column][vc_column width=”1/6″][/vc_column][/vc_row][vc_row][vc_column width=”1/1″][vc_row_inner columns_type=”1″ css=”%7B%22default%22%3A%7B%22background-color%22%3A%22linear-gradient%28180deg%2C%20rgba%2815%2C0%2C154%2C.3%29%200%25%2Crgba%280%2C90%2C128%2C.32%29%20100%25%29%22%2C%22border-radius%22%3A%2210px%22%2C%22border-style%22%3A%22solid%22%2C%22border-left-width%22%3A%225px%22%2C%22border-top-width%22%3A%225px%22%2C%22border-bottom-width%22%3A%225px%22%2C%22border-right-width%22%3A%225px%22%2C%22border-color%22%3A%22rgb%2825%2C%2053%2C%20110%29%22%7D%7D”][vc_column_inner width=”1/1″][us_text text=”Safeguard Your Organization” link=”%7B%22url%22%3A%22%22%7D” tag=”h2″ css=”%7B%22default%22%3A%7B%22text-align%22%3A%22center%22%2C%22font-size%22%3A%22%22%7D%2C%22laptops%22%3A%7B%22text-align%22%3A%22center%22%2C%22font-size%22%3A%22%22%7D%2C%22tablets%22%3A%7B%22text-align%22%3A%22center%22%2C%22font-size%22%3A%22%22%7D%2C%22mobiles%22%3A%7B%22text-align%22%3A%22center%22%2C%22font-size%22%3A%221.8rem%22%7D%7D”][us_text text=”Today With Dexpose” link=”%7B%22url%22%3A%22%22%7D” tag=”h3″ css=”%7B%22default%22%3A%7B%22color%22%3A%22_header_middle_text%22%2C%22text-align%22%3A%22center%22%2C%22font-size%22%3A%2240px%22%2C%22padding-left%22%3A%220px%22%7D%7D”][us_separator size=”small”][us_btn label=”Start Now” link=”%7B%22url%22%3A%22%23%22%7D” style=”30″ align=”center” icon=”fas|arrow-right” iconpos=”right”][/vc_column_inner][/vc_row_inner][/vc_column][/vc_row]