- Services
Learn
Dark Web monitoring
Gain Comprehensive Visibility Into Your Organization's Exposure On The Dark Web.
Breaches monitoring
Stay Ahead Of The Curve With Our Continuous Monitoring Service For Latest Breach Services.
Community
Attack surface mapping
Our Attack Surface Mapping Service Offers A Full Overview Of Your Exposed Assets.
Supply Chain Monitoring
Extend Your Risk Protection By Getting Immediate Insights Regarding Your Vendors' Breached Assets.
Resources
Brand Protection
Protect Your Customers From Phishing And Your brand from impersonation using our Brand protection services.
What's new
Dark Web monitoring
Gain Comprehensive Visibility Into Your Organization's Exposure On The Dark Web.
Dark Web monitoring
Gain Comprehensive Visibility Into Your Organization's Exposure On The Dark Web.
- Use Cases
- Partnership
Learn
MSPs Partnership
Discover New Avenues for Growth and Fortify Your SecurityOfferings through the Dexpose Partnership Program:Expanding Horizons and Enhancing Security Together.
Community
Offensive Security
Fortify network security with our concise cybersecurityuse cases and threat insights.
Resources
Data partnership (API)
Unlock the power of dark web intelligence with DeXpose's Data API integration, provide your cybersecurity product's clients with seamless access to real-time insights for enhanced cybersecurity.
- Free Tools New
Free Tools
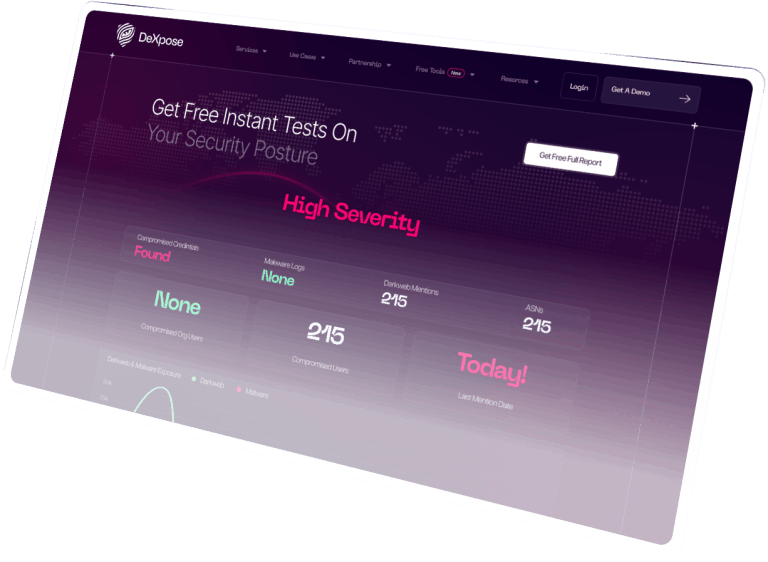
Free Darkweb Report
Unlock Valuable Insights Instantly: Receive an Immediate Comprehensive Exposure Report For Your Organization, Covering Dark Web Markets, Malware Logs, and Public Breaches, at No Cost.
Email Data Breach Scan
Check if your email has been mentioned in data breaches and analyze your organization's exposure in darkweb sources.
Oracle Breach Check
Search your company to see if it was mentioned in the alleged Oracle Cloud breach.
- Resources
Resources
Intel feeds
Stay current with real-time threat intelligence, ransomware attacks, and the latest breach reporting.
Blog
Explore the latest cybersecurity updates, expert insights, and industry news. Stay informed on threats, trends, and solutions.
Knowledge Hub
Access guides, resources, and expert materials on cybersecurity and dark web intelligence. Empower your team with actionable knowledge.
- Services
Learn
Dark Web monitoring
Gain Comprehensive Visibility Into Your Organization's Exposure On The Dark Web.
Breaches monitoring
Stay Ahead Of The Curve With Our Continuous Monitoring Service For Latest Breach Services.
Community
Attack surface mapping
Our Attack Surface Mapping Service Offers A Full Overview Of Your Exposed Assets.
Supply Chain Monitoring
Extend Your Risk Protection By Getting Immediate Insights Regarding Your Vendors' Breached Assets.
Resources
Brand Protection
Protect Your Customers From Phishing And Your brand from impersonation using our Brand protection services.
What's new
Dark Web monitoring
Gain Comprehensive Visibility Into Your Organization's Exposure On The Dark Web.
Dark Web monitoring
Gain Comprehensive Visibility Into Your Organization's Exposure On The Dark Web.
- Use Cases
- Partnership
Learn
MSPs Partnership
Discover New Avenues for Growth and Fortify Your SecurityOfferings through the Dexpose Partnership Program:Expanding Horizons and Enhancing Security Together.
Community
Offensive Security
Fortify network security with our concise cybersecurityuse cases and threat insights.
Resources
Data partnership (API)
Unlock the power of dark web intelligence with DeXpose's Data API integration, provide your cybersecurity product's clients with seamless access to real-time insights for enhanced cybersecurity.
- Free Tools New
Free Tools
Free Darkweb Report
Unlock Valuable Insights Instantly: Receive an Immediate Comprehensive Exposure Report For Your Organization, Covering Dark Web Markets, Malware Logs, and Public Breaches, at No Cost.
Email Data Breach Scan
Check if your email has been mentioned in data breaches and analyze your organization's exposure in darkweb sources.
Oracle Breach Check
Search your company to see if it was mentioned in the alleged Oracle Cloud breach.
- Resources
Resources
Intel feeds
Stay current with real-time threat intelligence, ransomware attacks, and the latest breach reporting.
Blog
Explore the latest cybersecurity updates, expert insights, and industry news. Stay informed on threats, trends, and solutions.
Knowledge Hub
Access guides, resources, and expert materials on cybersecurity and dark web intelligence. Empower your team with actionable knowledge.