Threat Actor Profile: Mustang Panda
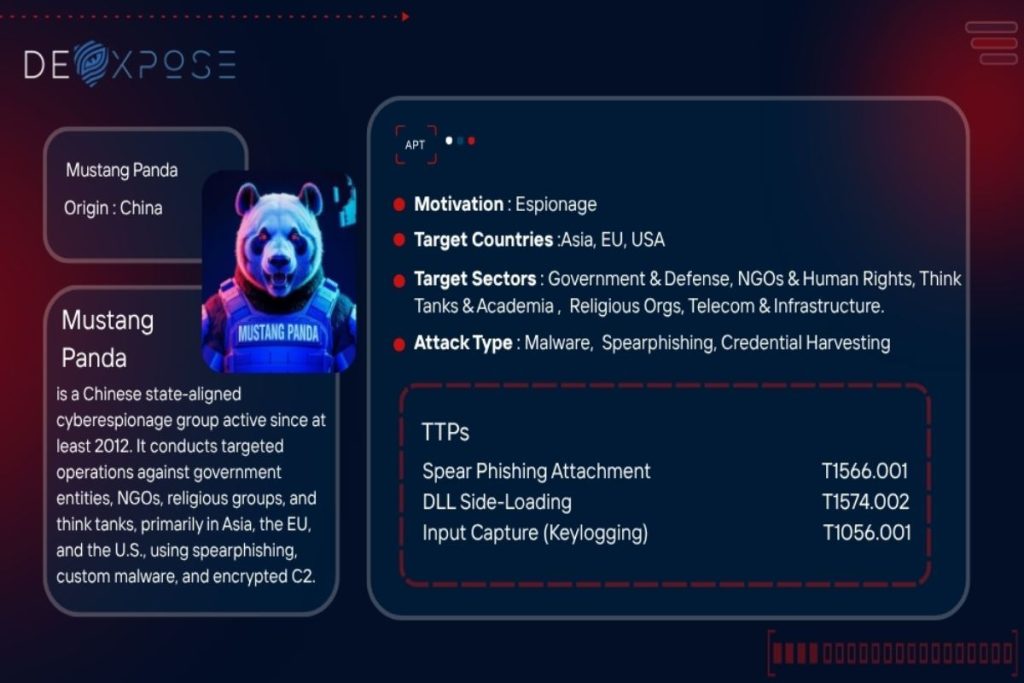
Mustang Panda is a highly persistent and adaptive Chinese state-linked cyber espionage group operational since at least 2012. Known by multiple aliases—including Red Delta, TA416, and Stately Taurus—this threat actor has consistently targeted entities of strategic relevance to the People’s Republic of China (PRC), using a sophisticated blend of spear-phishing, custom malware, and stealthy command-and-control […]
AnyDesk Clone Malware Drops Phemedrone Stealer Loader
On June 16, 2025, a suspicious domain impersonating AnyDesk — anydeske[.]icu — was reported on Twitter. The site served what appeared to be a legitimate remote access tool but actually delivered a malicious .NET loader. Further investigation revealed that the loader employed AES decryption, anti-analysis junk code, and evasion techniques to ultimately deliver Phemedrone Stealer. Attack Chain Overview […]
Uncovering Kimsuky APT Infrastructure | Threat Report

Summary Recently identified previously undetected Kimsuky (also known as Black Banshee) infrastructure through advanced pivoting techniques. Using HTTP header analysis, SSL Cert and JARM fingerprinting. We uncovered several IPs and domains, many of them were not flagged by VirusTotal at the time of discovery. Who is APT43 Kimsuky / Black Banshee? Kimsuky, also known as […]
Smishing Triad Impersonates Egypt Post in Phishing Scam

A recently observed phishing campaign impersonating Egypt Post (البريد المصري) has been attributed to the Smishing Triad, a well-documented cybercriminal group for their phishing (smishing) campaigns across multiple countries. The campaign impersonates Egypt Post, aiming to steal credentials and financial information through fraudulent SMS messages and phishing websites. Overview of the Campaign In early May 2025, multiple phishing SMS […]
FleshStealer Malware Report – Multivector Data Theft

Introduction FleshStealer is a sophisticated, modular, and obfuscated .NET-based information-stealing malware designed for comprehensive data exfiltration from Windows systems. Its architecture is built for scale and stealth, utilizing multithreading to simultaneously run multiple data harvesting routines with minimal system disruption. The malware targets a wide range of applications and services, including browsers, messaging apps, email […]
SalatStealer Malware Analysis and Data Theft Techniques

Introduction Salat Stealer is a stealthy malware developed in the Go programming language, designed to infiltrate systems and extract sensitive data. Once it infects a device, it gathers extensive system information, such as hard drive details, screen resolution, running processes, and active windows. One of its most alarming features is its ability to live-stream the […]
PureLogs malware analysis with data theft techniques

Introduction PureLogs is an advanced information stealer designed to extract credentials, session tokens, and system details while employing strong anti-analysis techniques. It encrypts stolen data using AES-256 before sending it to a remote Command & Control (C2) server. Capabilities and Functionality PureLogger is an advanced information stealer designed to exfiltrate a wide range of […]
Undetected .NET PE Injector Found on Archive Org
Introduction On February 11, 2025, Filescan.io shared a troubling discovery: a 6-month-old .NET PE injector had remained undetected on Archive.org, a platform widely used for archiving web content. The file was flagged as clean, allowing it to remain accessible for months. Capabilities This malware incorporates multiple techniques to evade detection and maintain persistence on infected systems. It employs the following capabilities: […]
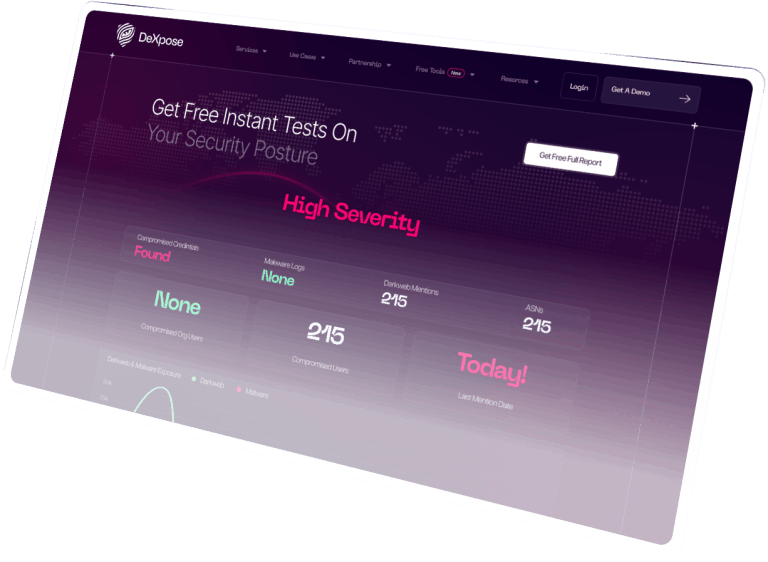
How Dark web Monitoring Protects Your business
Dark web monitoring is a crucial step for businesses to safeguard their sensitive data. This process involves scanning the dark web for compromised information, such as stolen credentials and proprietary data. Data breaches can have severe consequences, including reputational damage, financial losses, and operational disruptions. When employees reuse passwords across different platforms, it increases the […]
Email Breach Scan: How to Protect Your Personal Information

Email breaches pose significant risks to personal security when unauthorized users access email accounts or sensitive data. Often, leaked credentials can end up being sold on the dark web, leading to consequences like identity theft and financial loss. Public database breaches are common as hackers exploit vulnerabilities in organizations’ software systems. To protect your data, […]
In-Depth Technical Analysis of Lumma Stealer
Introduction Lumma is a sophisticated information stealer, written in C/C++, that has been active in the wild since at least August 15, 2022. The first publicly identified sample appeared on Malware Bazaar on December 20, 2022. By late 2022, the threat actor “Shamel,” operating under the alias “Lumma,” began promoting the malware on Russian-speaking cybercrime […]
Egyptian Organizations Darkweb Exposure Report

Are you wondering what kind of information about the Egyptian organizations the Darkweb has? As we all remember, the last few years were bad for many organizations regarding hacking and cyber threats. Digital shadows team published research indicating that there is ~24 Billion credentials pair available already on darkweb. These credentials sources vary from public database breaches […]