Summary
On October 30, 2025, the ransomware group incransom claimed responsibility for a cyberattack against
Evolve Mortgage Services (mrn3.com), a key player in the U.S. mortgage industry.
The group announced the theft of over 20 TB of sensitive data, threatening to disclose personal and financial information of thousands of clients unless their demands are met.
Incident Report
| Field | Details |
|---|---|
| Target | Evolve Mortgage Services |
| Domain | mrn3.com |
| Country | USA |
| Attacking Group | incransom |
| Date Reported | October 30, 2025 |
| Threat Actor Statement | “Introducing Evolve Mortgage Services, the old company name mrn3.com. We stole more than 20 TB of company data. Including 2TB of databases. This company refused to resolve the issue with us with the security of its customers’ data. This company does not care about the safety of its customers. They don’t care about leaks and disclosure of your data. We have all the data on all clients of both companies since 2016. SSN numbers, scans of client IDs, home and work addresses, personal, home and work phone numbers, FULL credit history about each client. Personal and confidential PII form information for thousands of citizens of the United States of America.” |
Recommended Security Actions
Ransomware attacks are increasingly targeting both enterprise and mid-sized organizations across all sectors. The following steps are critical to reduce impact and prevent future incidents:
- Monitor continuously: Use DeXpose’s dark web and infostealer monitoring platform to detect breached credentials, leaked databases, and threat actor chatter in near real-time—before damage spreads internally.
- Conduct a compromise assessment: Immediately initiate a full incident review to determine how attackers infiltrated your network, what data may have been exfiltrated, and whether any persistence mechanisms remain active.
- Validate your backups: Ensure that your backups are current, encrypted, and stored offline. Utilize immutable backup solutions to defend against ransomware encryption and deletion attempts.
- Apply threat intelligence: Integrate external threat feeds, including DeXpose-provided indicators of compromise (IOCs), into your SIEM or XDR platforms for real-time alerting and correlation.
- Harden employee defenses: Run phishing simulations and enforce multi-factor authentication (MFA) across all access points. Attackers often exploit weak or reused credentials sourced from the dark web.
- Engage professional response teams: Involve cybersecurity incident response experts, threat analysts, and legal counsel before initiating any dialogue with ransomware groups or ransom brokers.
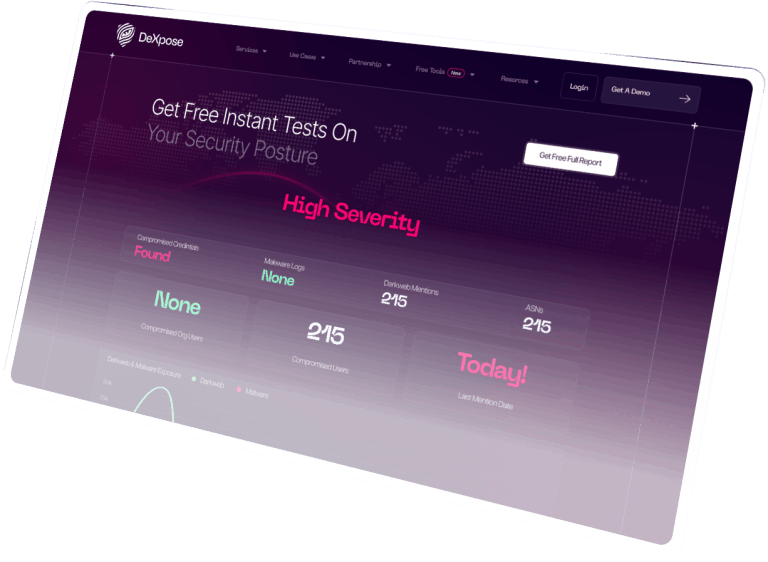
How DeXpose Helps You Stay Ahead
At DeXpose, we specialize in early detection and proactive defense. Our hybrid threat intelligence solution combines automated deep/dark web crawling, Telegram and forum monitoring, and real analyst verification to deliver:
- Continuous scanning of ransomware group leak sites, stolen credential markets, and malware log dumps
- Timely alerts for breaches linked to your domains, email addresses, and key personnel
- Intelligence correlation that connects leaked credentials to infostealer malware infections, often weeks before a public ransom demand
- Real-time visibility into supply chain and third-party exposures through passive surveillance of dark web channels
Don’t wait for public disclosure or ransom notices—gain visibility into your cyber exposure now.
-
Scan your domain for data breaches:
Free Dark Web Report -
Check employee or partner email exposure:
Email Data Breach Scan
Disclaimer
DeXpose does not engage in the exfiltration, hosting, redistribution, or purchase of stolen data. All breach information reported here is collected from publicly accessible dark web sources and threat intelligence platforms.
Our mission is to equip organizations with early-warning indicators, contextual threat insights, and actionable intelligence that help them secure their digital assets against evolving cyber threats.